EdTech Innovations – Gamification and Personalized Learning
In the ever-evolving landscape of education, two prominent trends, gamification and personalized learning, are reshaping the 21st-century classroom. EdTech innovations have seamlessly integrated these approaches to create dynamic and engaging learning environments that cater to the diverse needs of students. Gamification, the incorporation of game elements into non-game contexts, has emerged as a powerful tool to captivate students’ attention and foster a positive learning atmosphere. By leveraging elements such as competition, rewards, and interactive challenges, educators can transform traditional lessons into immersive experiences. This approach not only makes learning more enjoyable but also promotes collaboration, critical thinking, and problem-solving skills. Platforms and applications designed with gamification principles in mind allow students to progress at their own pace, providing a personalized learning experience that caters to individual learning styles.
Complementing gamification, personalized learning tailors educational content and methods to meet the specific needs and interests of each student. With the aid of advanced technologies and data analytics, educators can create adaptive learning paths, allowing students to navigate through curriculum materials at their own speed. This individualized approach not only accommodates diverse learning styles but also addresses varying levels of proficiency within a classroom. Adaptive learning platforms use algorithms to analyze students’ performance and adjust content delivery accordingly, ensuring that each student receives the support needed for optimal comprehension. The synergy between gamification and personalized 10 emerging trends in educational technology learning is particularly evident in EdTech solutions that seamlessly integrate both approaches. Educational games are designed to adapt to individual progress, presenting challenges that match students’ skill levels. These games often provide instant feedback, enabling students to learn from their mistakes and refine their understanding of concepts. The competitive and interactive elements of gamification motivate students to actively participate in their learning journey, fostering a sense of autonomy and ownership over their education.
Furthermore, the integration of artificial intelligence AI in EdTech has elevated personalized learning to new heights. AI algorithms analyze vast amounts of data, including students’ performance, preferences, and learning patterns, to generate insights for educators. This data-driven approach allows for the identification of areas where students may need additional support or challenges, enabling teachers to tailor their instruction more effectively. As a result, the classroom becomes a dynamic and responsive ecosystem that caters to the unique needs of every learner. In conclusion, the fusion of gamification and personalized learning in the 21st-century classroom represents a transformative leap in education. EdTech innovations that embrace these approaches create an engaging and adaptive environment where students not only acquire knowledge but also develop essential skills for the future. By harnessing the power of gamified learning experiences and tailoring content to individual needs, educators can unlock the full potential of each student, paving the way for a more inclusive and effective educational landscape.
TikTok Voice Generator – The Ultimate Tool for Memes, Comedy, and More
In the ever-evolving landscape of social media, TikTok has emerged as a powerhouse platform that thrives on creativity, humor, and engagement. As it continues to grow in popularity, content creators are constantly on the lookout for tools and features that can enhance their content and captivate their audience. One such tool that has gained prominence is the TikTok Voice Generator, which has become the ultimate resource for memes, comedy, and various other forms of creative expression. The TikTok Voice Generator is a user-friendly tool that allows creators to manipulate their voices, transforming them into various characters, accents, and tones. This tool has opened up a world of possibilities, enabling content creators to push the boundaries of humor and creativity on the platform. One of the most prominent uses of the TikTok Voice Generator is in the creation of memes. Memes are a cornerstone of TikTok culture, and they often rely on humor and satire. With the voice generator, creators can add a hilarious twist to their videos by impersonating famous personalities, mimicking iconic movie quotes, or creating entirely new characters with distinct voices.

This not only adds a comedic element but also helps in making the content more shareable and relatable to a wider audience. Comedy is another genre that has greatly benefited from the TikTok Voice Generator. Comedians and humorists can now explore a wide range of comedic styles, from slapstick to dry humor, by altering their voices to suit the tone of their content. Whether it is delivering one-liners in a deep baritone or impersonating cartoon characters with high-pitched voices, the tool empowers creators to experiment with their comedic timing and delivery. The TikTok Voice Generator has also become a valuable resource for educational content. Many educators and tutors are leveraging this tool to engage their students by adopting different personas or accents during lessons. This not only makes learning more enjoyable but also aids in conveying complex concepts effectively. Whether it is teaching history with the voice of a historical figure or explaining science in the style of a famous scientist, the TikTok Voice Generator makes learning fun and memorable.
In addition to memes, comedy, and education, the tiktok voice generator has found applications in various other creative endeavors. Musicians can use it to experiment with vocal effects and harmonies, adding depth and uniqueness to their compositions. Storytellers can bring their characters to life with distinct voices, immersing their audience in captivating narratives. Even businesses are exploring the potential of this tool to create memorable advertisements and promotional content. Furthermore, the TikTok Voice Generator has contributed to fostering a more inclusive and diverse community on the platform. Creators can use it to explore and celebrate different accents and dialects, breaking down linguistic barriers and promoting cultural exchange. This not only enriches the content on TikTok but also promotes a sense of global unity and understanding. While the TikTok Voice Generator offers immense creative potential, it is essential for creators to use it responsibly and ethically. It is crucial to avoid any content that perpetuates stereotypes, promotes hate speech, or violates TikTok’s community guidelines. Like any tool, it should be used to uplift and entertain, rather than harm or offend.
Optimize Your System Stability by Repairing Mfc140u.dll Errors
Mfc140u.dll errors can be quite frustrating as they can disrupt the stability and functionality of your system. The Mfc140u.dll file is a component of the Microsoft Visual C++ Redistributable package, which is essential for running certain applications and programs on your computer. When this file encounters issues or becomes corrupted, it can lead to various error messages and system instability. One common error associated with Mfc140u.dll is the missing file error, which occurs when the operating system is unable to locate the DLL file required to run a specific program. This can happen due to accidental deletion, malware infection, or incorrect installation of software. Another error is the not found error, which suggests that the file is either missing or inaccessible. Additionally, you might encounter a file is corrupted error, indicating that the DLL file is damaged or incompatible with your system.
To optimize your system’s stability and resolve Mfc140u.dll errors, there are several recommended steps you can take. First, ensure that your system is free from malware by running a thorough antivirus scan. Malicious programs can infect and corrupt DLL files, leading to errors. If any malware is detected, remove it promptly. Next, consider reinstalling the Microsoft Visual C++ Redistributable package. This package includes the necessary DLL files, including Mfc140u.dll, to run certain applications. Download the latest version of the package from the official Microsoft website and follow the installation instructions. This will replace any missing or corrupted DLL files and ensure their compatibility with your system. In some cases, manually registering the Mfc140u.dll file can help resolve errors. To do this, open the Command Prompt as an administrator and type regsvr32 Mfc140u.dll without the quotes. Press Enter and you should receive a confirmation message indicating successful registration. If the above steps do not resolve the issue, consider performing a system restore to a previous point when your system was functioning properly.
System restore allows you to roll back your computer’s settings and configuration to a previous state, effectively undoing any recent changes that may have caused the DLL errors. Finally, keeping your system up to date with the latest Windows updates and patches is crucial for overall stability. Microsoft often releases updates that address known issues and provide bug fixes for DLL files. Ensure that automatic updates are enabled, or manually check for updates regularly to keep your system optimized. In conclusion, mfc140u.dll errors can significantly impact your system’s stability and hinder the proper functioning of applications. By following the steps outlined above, you can effectively repair these errors and optimize your system’s performance. Remember to exercise caution when downloading files from the internet and regularly maintain your system’s security to prevent DLL-related issues in the future.
The Different Attributes Of Getting the Television Licence For Everyone
Television trivia is most likely so popular now for the reason that events of just about every home using a television are gone, and now most residences have several. Prior to the beginning of the internet, television was the main distribution technique for the two enjoyment and knowledge, and yes it nonetheless remains to be the implies in which a lot of people receive both those things. The television initially grew to be accessible to the general public in different parts of the globe in the late nineteen thirties. In the early days of television, broadcasts and packages only managed in monochrome. There are very early creations which were effective at broadcasting in color just before the TV had develop into a house appliance, even so none succeeded. RCA took over as the initially firm to produce color TV units accessible. The hue TV did not become the standard in the majority of houses up until the sixties nevertheless.

The developments in the technology right behind television packages have carried on advancing. The advent of the flat screen technology started out the cross over to televisions which may screen in increased quality, but LCD and Plasma screens are actually the standard generally in most residences. The present breakthroughs have been in the changing of television broadcasts from an analogue to digital file format. Furthermore, broadcasting in high-definition signal is currently offered by most main networks, and every satellite and cable provider provides hi-def channels. Nowadays, television and movies may be streamed, nearly seamlessly, via your Internet broadband connection. Virtually each significant television reports wall plug has bothersome movie home windows which simply automatically enjoy inside the correct or remaining border of the home web page, or even smack dab right in the middle. Video clip has become this type of common fixture of your Internet which we now virtually accept it with no consideration. Internet TV is actually the opportunity to look at movie streams on the Internet.
With the rise in internet connection rates, advances in technology, it can be now capable of freely access. Totally free Internet Television design is based on the same writing design that is available on the Web: it permits access to an available program, anyone can access, use and make for, with the development of available resource software, wide open requirements and formats. But, a lot of people also watch television too, regardless of whether by way of satellite or cable, due to the fact sitting on the couch facing cancel TV licence is often better than curling up and squinting in the much smaller screen of your laptop, tablet computer or smart phone. Television trivia is normally with regards to typically the most popular viewing events. There are numerous styles of television, news, sports activities, reality, extraordinary encoding and sitcoms, and particular classes persistently get more audiences than other. After all those broadcast there are lots of other shows that contain positioned in the top rated most seen broadcasts.
Distinctions between Premium Security and Internet Security
The fact of the matter is these projects are not as muddled as you would naturally suspect. Truth be told, you can get one bundle that incorporates every one of them and save yourself truckload of cash and stress simultaneously. Premium security programming goes by many names and they incorporate total, outrageous, extreme, super-suites, ultra, mega and absolute. So it incorporates all buyer level security programming in one, with every one of the highlights and apparatuses you will require. Yet, internet security programming incorporates a significant number of a similar security projects, elements and devices. What is more, you will have the option to shield your PC from the very dangers that a top notch security programming program is intended for. Be that as it may, they truly do have a couple of contrasts and before you pick one, we suggest you look at their highlights and capacities to settle on the ideal decision. Before we take a gander at their disparities, we need to feature a couple of their likenesses.

Similitudes
Like internet security programming, premium security incorporates antivirus, hostile to spam, firewall and antispyware insurance. These four assurance programs have their own independent adaptations. Furthermore, each fills a particular need and eliminates specific kinds of dangers. Joined, they are an impressive power and guarantee that your PC is safeguarded on all points in pixelroo.com. Premium and internet security programs additionally have highlights that you will not get in independent projects. A portion of these increases incorporate information reinforcement, parental controls, gamer modes and hostile to phishing devices.
Contrasts
One clear distinction between these two suites is cost. By and large, premium security is about £15 more costly than internet security programming. There are a couple of less expensive premium projects like Zone Alarm Outrageous Security who likewise consistently offer limits as well. Yet, generally internet security is a lot less expensive and BitDefender is as of now retailing at £29.99. Is the Exceptional security cost supported? Well that relies upon the elements and devices you are searching for; which carries us to the subsequent distinction, which is found in the apparatuses they offer. Premium security has PC Utility Apparatuses which are intended to perform fixes on your PC and wipe out brief internet records. These highlights are strong and upgrade your general security. One of the noteworthy devices is Accelerate Start which is a progression of changes that rush your PC and operating system fire up time. Likewise, all top notch security suites incorporate protection, information reinforcement, online capacity, and firewall and PC framework utilities; while a couple of internet security suites incorporate this multitude of projects and they are not as successful.
Rundown
The facts really confirm that the entire is more noteworthy than the amount of its parts and this is clear in premium and internet security bundles. The independent projects additionally found in these two suites are first class, yet together they give amazing security. So your decision between the two will rely upon your own need or inclinations.
Free Bing Ads are more confidential for users
It is likely one of the most blazing selling digital books ever, and may very well remain famous for some time to turn into the most sizzling digital book of all time. Yet, what makes Get Bing ads Free so snappy and infectious that individuals tingle to have it and public interest consumes far and wide in the brush? Might it at any point be its timing; coming at a period when some web advertisers can’t successfully involve Bing ad Words in their missions due to forcing offers and fierce opposition. Is it since it implied on double crossing a goliath organization that rakes in many millions in US Dollars every day?
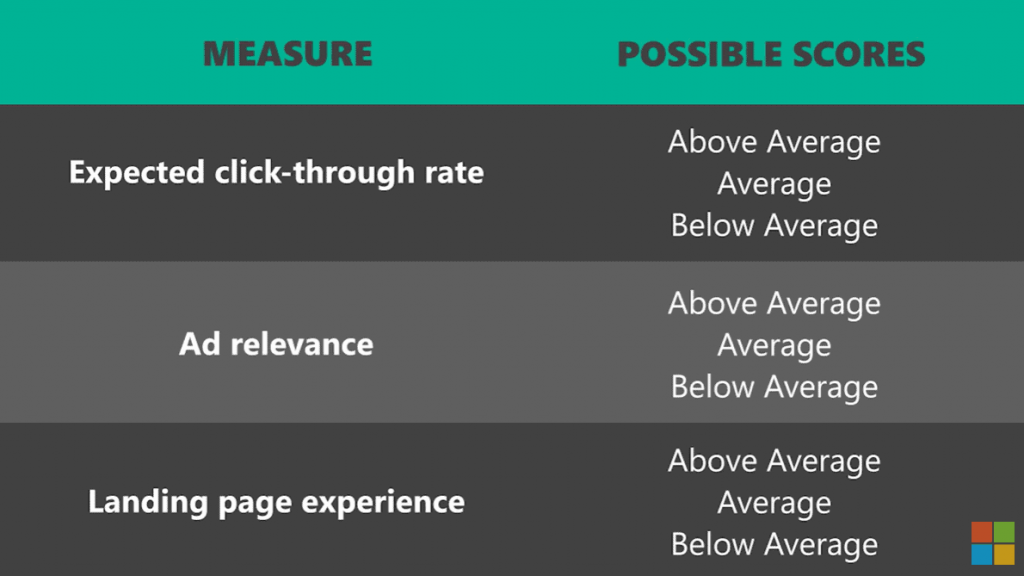
What really makes this book a dazzling achievement is that, it was made in exactly the same way, and through similar cycle best organizations are made. Borne out of a basic thought, approved by statistical surveying, carried out and executed against an unshakable arrangement. Yet, what makes the methodology work is its having the option to fulfill one essential showcasing guideline; providing a market with an apparent result of significant worth, 必应广告质量得分 and sold with areas of strength for a commitment that is to serve or address that requirement for which it is bought. In the wake of finding an item for what it’s truly worth, there must be the fulfilled and the bamboozled; the blissful and the troubled; or the “I made out really well” and the “is there an unconditional promise” gatherings.
Yet, as any piece of work is generally abstract, and everyone special; we are completely qualified for the subsequent emotional impact of the experience of perusing the book, and consequently think about it for ourselves in contrast to our own singular standards. Yet, permit me to talk from my own insight of perusing Get Bing ads Free. Allow me to begin by saying that I was blissful to get it, then, at that point, frustrated, then “not terrible, but not great either” fulfilled after understanding a few little and minor insights… we underestimate or neglect. Wise, disrespectful… what’s more, yes I was somewhat dazzled. Anyway there was nothing truly new introduced, no cutting edge thought or idea or record breaking accomplishment with the exception of likely in the many millions in deals produced by applying those standards. The creator concedes that there is actually the same old thing as he basically utilizes old and laid out methodologies and gives an illustration of how other business are utilizing that system for their potential benefit.
Reasons Why Your Business Needs Server Support
Albeit every one of the parts of your association specialized arrangement is significant in taking care of your business competently, server support is the absolute most significant security to have. That is on the grounds that servers – whether critical servers or modest ones are your road of correspondence within and beyond your association. At the point when a server is down, you will be unable to get to your email, your significant work files may be unavailable, or you might even not have the option to sign in. It is normal for representatives to be totally unfit to work. As a matter of fact, when significant servers are down, business can crush to a sudden end. Servers are the foundation of all business computer networks. Servers store information, permit admittance to the network, have applications, and store data. Whether your company is a little company with just an email server or a huge venture with numerous data communities, having the right server support is essential to everyday productivity.
Dissimilar to work stations, servers are computers that are gotten to by numerous individuals simultaneously. Since servers play various parts relegated to them, there are a heap of various issues that can happen in the event that a server is slow or fizzling. For instance, a sluggish space server might imply that individuals cannot sign in to their computers in an opportune design, causing long sign in times and diminishing productivity. Issues with a file server could imply that individuals cannot get to the files that have been put away on the network, which likewise implies diminished productivity. An email server that experiences an equipment disappointment could have horrendous outcomes, bringing about a part of users or more terrible, and a whole company being not able to get to, send, or get email. Any website works from, and is on, a server some place on the planet. That server is simply one more computer, yet a great many people’s websites are on servers that are in shared facilitating facilities.
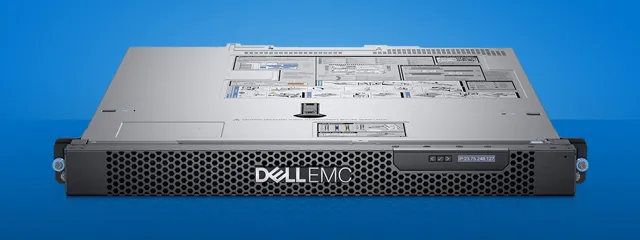
Different individuals, all simultaneously, frequently access servers. At the point when a server goes down, it is logical that more than one individual is impacted by the blackout, and the more drawn out a server is down, the more drawn out productivity will be impacted. They can likewise monitor and keep up with servers to assist with guaranteeing that issues will not happen from here on out. By guaranteeing that may chu dell poweredge is all in great shape and that software is refreshed and fixed to forestall security breaches or other software related dangers, server support can assist with ensuring that your servers stay up and useful, permitting your business to continue to run. Having solid server support can keep these situations from occurring. At the point when a business has server support that they can depend on, they realize that their servers will be dealt with by experts as fast as could be expected.
WhatsApp GB – A Powerful Contender to WhatsApp
Text messaging apps are getting to be very popular as increasing numbers of individuals are making use of them to stay in contact with friends and relations. There are numerous texting apps which can be now available. Many of them cost nothing while many expense a bit of cash. Since the demands of users increase, the applications way too are becoming a lot more stylish. Consumers are now capable of deliver images, audio and video as part of their messages. Nonetheless, with additional amount of people by using these apps, you will discover an increased requirement for personal privacy and security. No person wishes to make use of an application which is lacking in level of privacy or lacks adequate safety.

Another necessary thing to consider when selecting which mobile app to work with is its pace. Given that customers could share audio and video files together, they require high speed interaction. WhatsApp gb is a new entrance in the market of WhatsApp gb concept programs. It was actually unveiled in August 2013. Its reputation is speedy rising since it has so many characteristics. It offers swift conversation and stability. As a result of each one of this stuff, end users are having a satisfying experience with by using this mobile app to remain in touch making use of their friends and relations. Among the many superb options that come with WhatsApp gb is the capability to group chat with practically 200 individuals at a time. It is simple to send messages to numerous folks as well as retailer messages you get from their website. Its text messaging process performs fast since it has decentralized facilities distribute around the world. This ensures that whichever information you deliver can journey to another individual in every spot on the planet in very little time.
WhatsApp GB also will pay a lot of emphasis on level of privacy and safety through the transfer of communications. It makes use of higher-level file encryption to provide level of privacy. This resource will be able to supply top class stability regardless if transferring great quantities of web data. The advantage of WhatsApp gb is the fact that it is able to job even on much weakened mobile connections, which makes it considerably more reliable than many of its opponents. Individuals can discuss photographs, video tutorials and other media files as large as 1 Gigabyte. All of these points make WhatsApp GB a powerful rival to WhatsApp.
Understanding the VPN Services Requirements
VPN services permit you to safely interface with any server on the Web. The manner in which they work is by giving you an IP address that is totally anonym zed and by scrambling all of your correspondence with the VPN server. To work with this, they typically offer a few distinct servers situated across a wide geographic region. To get yourself attached with the right VPN service, you ought to try to comprehend the rudiments of how they work and what you can anticipate from various kinds of VPN services.
Survey Your Requirements
The primary thing you need to decide is the amount you’re probably going to utilize the VPN service. Certain individuals are probably going to utilize the service practically constantly and others will most likely possibly use it when they are utilizing sure projects that they need to keep secure. On the off chance that you intend to utilize the VPN service constantly, you’ll need a service that offers you a lot of transmission capacity. There are services out there that offer limitless data transmission and, assuming you intend to utilize your VPN service in any event, for easygoing web perusing, you need to get one of these limitless plans. On the off chance that you just have to utilize your VPN service to connect to one specific server or for one specific program, you can get an incredibly diminished measure of data transfer capacity. The low-finish of data transfer capacity contributions typically begins at around five gigabytes each month. Assuming you’re keen on one of these lower end plans, you’ll wind up setting aside cash and, gave you get sufficient data transfer capacity, you’ll in any case get sufficient service to verify that you can participate in safe Web perusing as the need might arise.

You’ll likewise need to verify where the VPN service has servers found. A portion of these services have a colossal number of servers situated all through the world and others just have a couple. In a perfect world, you ought to connect to a server that is near your geological area. This guarantees that you’re getting the best speed and execution out of the network. Verify that you verify whether there is any distinction between the services accessible on every one of the various servers given by the network. There generally isn’t, yet it’s in every case great to make certain.
There are many extra elements that VPN services like to incorporate to make their item more alluring. With these elements, verify that getting you’re paying for out of them that you’ll really utilize any extra services that you choose to buy. At times, you might have the option to get by with a more affordable VPN service, as the extra elements will not be very useful to you. It simply relies on your requirements and check here for more useful information https://rubyvpn.com/.
A Glance at Against Virus Projects and secure the monetary programming
 The consistent writing and circling of PC viruses and of frenzy about them concedes the venders of business antivirus programming a monetary interest in the continuous presence of viruses. A couple guesses that antivirus organizations have monetary connections to virus creators, to produce their own commercial center, however there’s no proof that we are aware of. A portion of the antivirus programming can diminish PC execution extensively. Clients can incapacitate the antivirus insurance to move past the exhibition misfortune, subsequently raising the risk of contamination. For the best insurance the antivirus programming expects to be empowered consistently frequently at the expense of more drowsy execution. It is likewise exceedingly vital to perceive that an individual should not have more than one antivirus programming bundle set up on a singular PC at some random time.
The consistent writing and circling of PC viruses and of frenzy about them concedes the venders of business antivirus programming a monetary interest in the continuous presence of viruses. A couple guesses that antivirus organizations have monetary connections to virus creators, to produce their own commercial center, however there’s no proof that we are aware of. A portion of the antivirus programming can diminish PC execution extensively. Clients can incapacitate the antivirus insurance to move past the exhibition misfortune, subsequently raising the risk of contamination. For the best insurance the antivirus programming expects to be empowered consistently frequently at the expense of more drowsy execution. It is likewise exceedingly vital to perceive that an individual should not have more than one antivirus programming bundle set up on a singular PC at some random time.
This may seriously handicap your PC and cause extra harm. It is vital for briefly cripple PC virus security while you set up significant updates, for example, Windows Administration Packs or refreshing designs card drivers. Having antivirus assurance working simultaneously as establishment of a significant update would hold the update back from introducing accurately or in any event, introducing by any means. When you in all actuality do decide to purchase antivirus programming, the plan could incorporate a provision that your membership will be naturally reestablished, and your Visa consequently charged at the time you should restore without you approving it. For example, MacAfee anticipates that you should buy in something like sixty days preceding the termination of your current membership, At whatever point that is the situation, the endorser could challenge the accuses of the charge card backer,
However this strategy is presumably to be of no assistance to you if indeed the supporter had cleared such a continuous installment authority. A couple of hostile to virus programs are in actuality malware taking on the appearance of against virus programming. It is for your mobile security potential benefit to learn that the product bundle which you are downloading is actually a certified antivirus program. A couple of business antivirus programming programs hold adware, For example, the home/private company version of a CA Hostile to Virus 2008 displays a promotion for CA items at whatever point the work area is opened after a timeframe while the figuring machine is not dynamic. It will be nothing unexpected when PC viruses that plague the work area and the PC quickly move to mobile gadgets. Progressively dealers in this space are giving answers for battle this.